The shadowy world of the dark web has always enticed cybercriminals seeking anonymity. OnionLinks, a notorious network known for its intricate structure, serves as a nexus for illicit activities ranging from drug trafficking to the distribution of sensitive data. Investigators venture on perilous journeys into this virtual underworld to unravel criminal organizations, expose their operations, and safeguard unsuspecting victims.
OnionLinks's unique topology presents a formidable obstacle to law enforcement. Its robust safeguards hide the more info identities of users and their activities, making it a bastion for anonymity. However, cybercrime analysts are constantly evolving their methods to penetrate this digital fortress.
- Cutting-edge software
- Surveillance operations
- Online crime analysis
By utilizing these tools and expertise, investigators can unmask the perpetrators behind OnionLinks, disrupt their criminal enterprises, and bring vindication to victims. The fight against cybercrime on platforms like OnionLinks is an ongoing struggle demanding unwavering resolve.
Unmasking the Dark Web: The Role of OnionLinks in Anonymous Communication
The dark/shadowy/hidden web, a realm shrouded in mystery/secrecy/anonymity, has become synonymous with illicit activities/transactions/operations. Within this digital underworld, OnionLinks/Tor Links/Darknet Addresses emerge as the key/essential/vital facilitators of anonymous communication. These peculiar hyperlinks/URLs/addresses operate on a unique/specialized/encrypted network called Tor, allowing users to traverse/navigate/browse the dark web with a degree of obscurity/invisibility/anonymity.
Each OnionLink functions/operates/works as a series of layers/encryptions/tunnels, effectively masking/hiding/concealing the user's true identity/location/IP address. This multi-layered/complex/sophisticated approach to encryption makes it extremely/highly/remarkably difficult for intermediaries/authorities/hackers to intercept/trace/monitor communications, fostering an environment where users can interact/communicate/engage with a level of confidentiality/privacy/security that is unavailable/rare/limited on the surface web.
OnionLink Directory
Venturing into the depths of the internet often feels like traversing a labyrinth. Charting a course through this digital maze can be daunting, especially when seeking out hidden services known as Onion Links. That's where the OnionLink Directory comes in, acting as your compass to these often-overlooked corners of the web. This curated database offers a glimpse into the world of hidden services, categorized by function and purpose. Whether you're investigating for privacy, alternative forums, or even specialized content, the OnionLink Directory can be your dependable guide through this often-misunderstood realm.
- Keep in mind: The nature of hidden services means that accessing them carries inherent potential dangers. It's crucial to prioritize your security and exercise awareness when navigating this digital frontier.
Exploring the Dangers of OnionLinks: From Black Markets to Malware Distribution
The underworld web, often accessed via OnionLinks, presents a dangerous landscape. While it offers concealment, it has become a breeding ground for illicit activities. Malicious actors exploit OnionLinks to facilitate black markets for everything from stolen credentials to illegal products. Furthermore, these addresses can be used to transmit malware, infecting unsuspecting users' systems. The risk of encountering harmful content or becoming a victim of cybercrime while navigating OnionLinks is considerable.
Unveiling Secrets Through OnionLink Analysis
The digital landscape is a complex network of interconnected information, often cloaked in layers of anonymity. Uncovering the secrets hidden within requires specialized tools and techniques. One such method is OnionLink Analysis, a powerful approach that delves into the links between seemingly isolated entities. By tracing these lines, analysts can reveal hidden patterns and connections, shedding light on otherwise elusive information.
- Additionally, OnionLink Analysis allows investigators to identify potential threats by visualizing the flow of data. This can be vital in addressing cybercrime, criminal networks, and other types of online peril.
- By means of OnionLink Analysis, researchers can also achieve a deeper knowledge into complex structures. This has effects in various fields, such as social sciences, where identifying underlying relationships can provide valuable knowledge
Nevertheless, OnionLink Analysis is a demanding process that requires advanced knowledge and skills. Analyzing the vast volumes of data generated by these networks can be laborious.
Safe and Private? The True Face of OnionLinks in the Digital World
OnionLinks, often referred to as Tor links, present a complex proposition: can they truly ensure both security and anonymity in the ever-evolving digital landscape? While the technology behind them is built to hide user information, the reality is far more subtle.
A multitude of variables can modify the level of security and anonymity offered by OnionLinks. Errors on the user's end, or even within the Tor system itself, can reveal sensitive details. Moreover, skilled attackers may employ advanced techniques to break through these safeguards.
Therefore, it is crucial for users to approach OnionLinks with a healthy dose of vigilance. A thorough understanding of the system and its boundaries is essential. Employing additional privacy measures, such as strong passwords, can further minimize the risks associated with OnionLinks.
 Jonathan Lipnicki Then & Now!
Jonathan Lipnicki Then & Now! Josh Saviano Then & Now!
Josh Saviano Then & Now! Hailie Jade Scott Mathers Then & Now!
Hailie Jade Scott Mathers Then & Now! Lacey Chabert Then & Now!
Lacey Chabert Then & Now!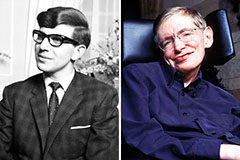 Stephen Hawking Then & Now!
Stephen Hawking Then & Now!